Overview
SSO/SAML is only available on Production and Enterprise plans.
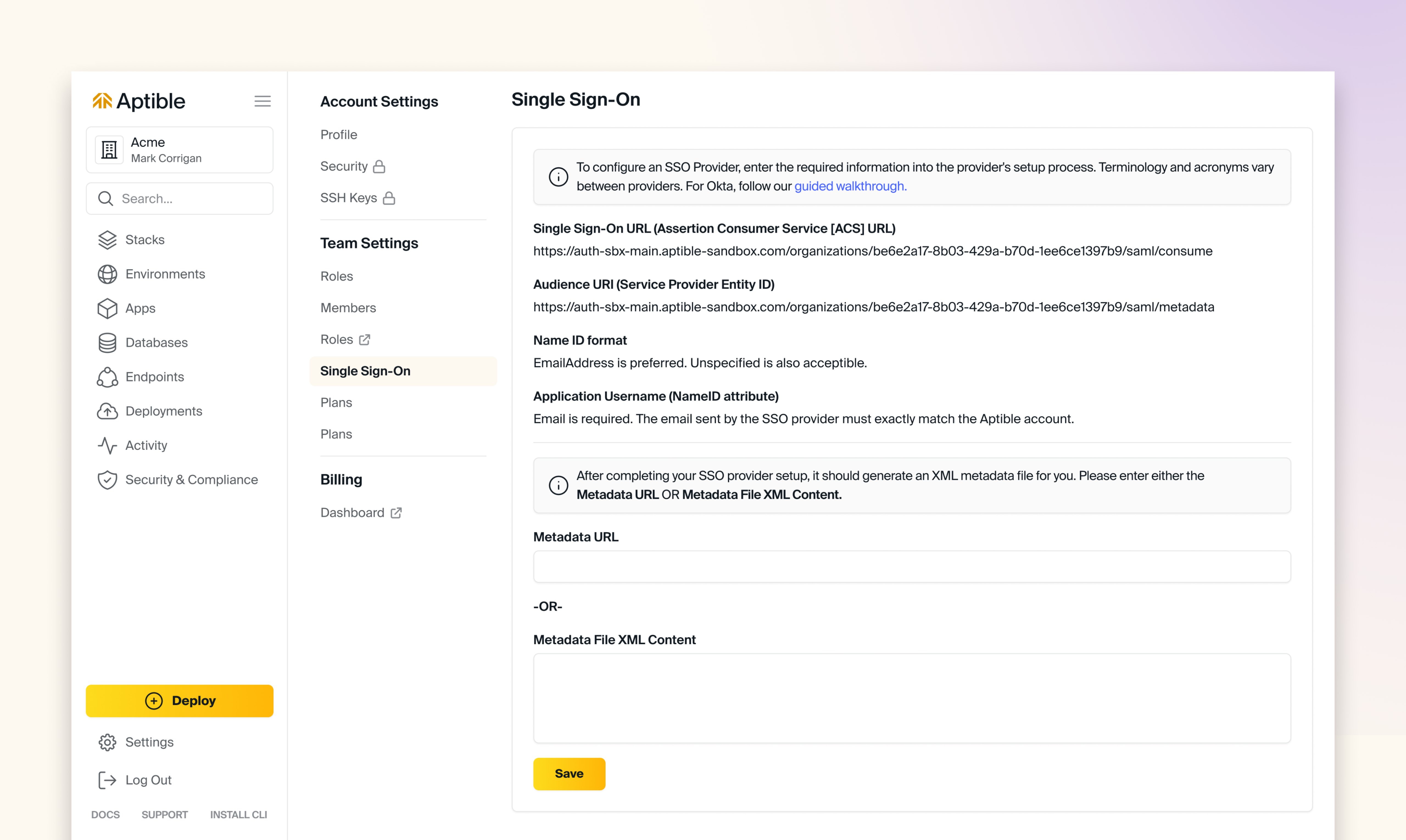
How to setup Single Sign-On (SSO)
Organization Login ID
When you complete Single Sign On Provider Setup, your organization’s users can use the SSO link on the SSO login page to begin using the configured SSO provider. They must enter an ID unique to your organization to indicate which organization they want to access. That ID defaults to a randomly assigned unique identifier. Account owners may keep that identifier or set an easier-to-remember one on the SSO settings page. Your organization’s primary email domain or company name makes a good choice. That identifier is to make login easier for users. You will have to distribute the ID to your users so they can enter it when needed. To simplify this, you can embed the ID directly in the URL. For example,https://dashboard.aptible.com/sso/example_id. Users can then bookmark or link to that URL to bypass the need to enter the ID manually. You can start the login process without knowing your organization’s unique ID if your SSO provider has an application “dashboard” or listing.
Require SSO for Access
WhenRequire SSO for Access is enabled, Users can only access their organization’s resources by using your configured SAML provider to authenticate with Aptible. This setting aids in enforcing restrictions within the SSO provider, such as password rotation or using specific second factors.
Require SSO for Access will prevent users from doing the following:
- Users cannot log in using the Aptible credentials and still access the organization’s resources.
- Users cannot use their SSH key to access the git remote.
CLI Token for SSO
To use the Aptible CLI with Require SSO for Access enabled, users must:- Generate an SSO token.
- In the Aptible Dashboard, select the user’s profile on the top right and then “CLI Token for SSO,” which will bring you to the CLI Token SSO settings page.
- Provide the token to the CLI via the
aptible login --sso $SSO_TOKENcommand.
Invalidating CLI Token for SSO
- Tokens will be automatically invalidated once the selected duration elapses.
- Generating a new token will not invalidate older tokens.
- To invalidate the token generated during your current session, use the “Logout” button on the bottom left of any page.
- To invalidate tokens generated during other sessions, except your current session, navigate to Settings > Security > “Log out all sessions”
Controlling CLI Token Lifetime
To limit how long CLI tokens remain valid when using SSO:- Require SSO for all users — Enable Require SSO for Access (described above).
- Configure session duration in your Identity Provider — Set a shorter max session duration in your IdP (e.g., Google Workspace). This is where the limit is enforced.
Exempt Users from SSO Requirement
Users exempted from the Require SSO for Access setting can log in using Aptible credentials and access the organization’s resources. Users can be exempt from this setting in two ways:- users with an Account Owner role are always exempt from this setting
- users added to the SSO Bypass Allowlist
Require SSO for Access is enabled.
Account Owners and users on the SSO Bypass Allowlist can generate CLI tokens directly through Aptible (via username/password login) even when Require SSO is enabled. These users may create tokens with a lifetime of up to 7 days. There is no mechanism to reduce this 7-day limit at the organization level. To enforce shorter token lifetimes, we recommend limiting the number of users granted Account Owner access.
Require SSO for Access settings, but there are some use cases where it is necessary; some examples include:
- to allow users to use their SSH key to access the git remote
- to give contributors (e.g., consultants or contractors) access to your Aptible account without giving them an account in your SSO provider
- to grant “robot” accounts access to your Aptible account to be used in Continuous Integration/Continuous Deployment systems

